Table of Contents
ToggleThe Invisible Predator:
Is India Winning the War
Against Digital Child Sexual Exploitation?
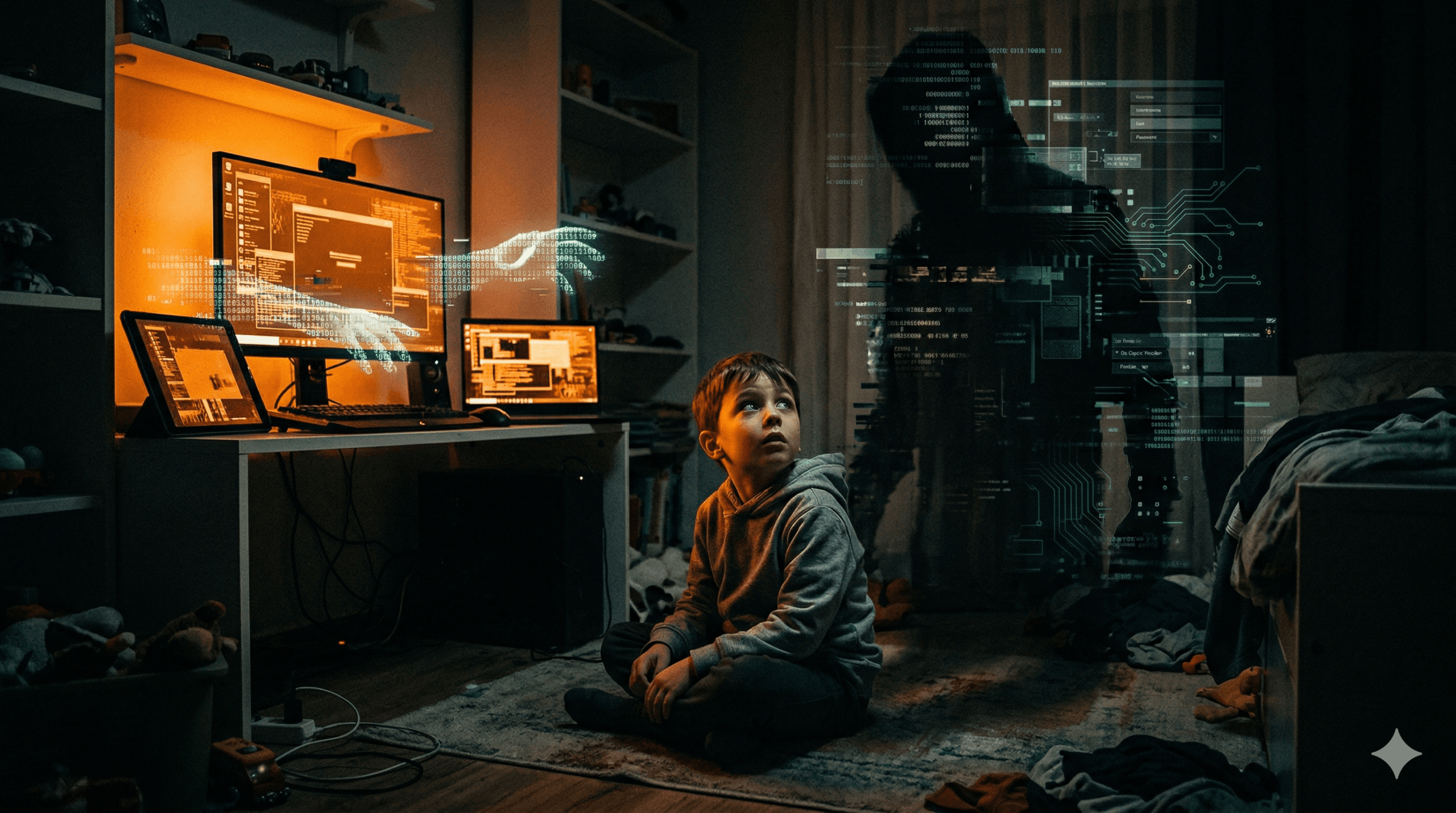
A screen is not a shield. In 2026, Digital Child Sexual Exploitation is the greatest threat to India's children. Behind every 'innocent' app lies a potential gateway for abuse. Are we looking closely enough?
"The internet is a public square where the most vulnerable walk without a guardian. We must ensure the law travels wherever the data goes."— Adv. Mamta Shukla · Child Rights & Legal Advocate
In 2026, a child's bedroom is no longer a guaranteed safe haven. With a single tap, a predator located thousands of miles away can bypass locked doors, security guards, and vigilant parents, stepping directly into a child's world. Digital Child Sexual Exploitation (DCSE) is the silent, pervasive epidemic of our time, evolving faster than the hardware that facilitates it.
As India's digital footprint expands at a breakneck pace, the intersection of rapid internet penetration and vulnerable youth has created a hunting ground. The traditional warning to "never take candy from a stranger" has become dangerously obsolete. Today, the candy is an in-game currency, a compliment on a social media reel, or a seemingly harmless request for a photo.
We are fighting a 21st-century war using 20th-century parenting. The threat has digitized; our defenses must do the same.
This guide breaks down the complex anatomy of Digital Child Sexual Exploitation, pairs it directly with the protections afforded under the Protection of Children from Sexual Offences (POCSO) Act and the IT Act, and delivers actionable, non-negotiable steps for parents, educators, and guardians.
Part I: The Modern Anatomy of DCSE
To defend against an enemy, you must first understand how they operate. Predators in 2026 do not rely on brute force; they rely on psychological manipulation. We categorize the modern threat of Digital Child Sexual Exploitation into three distinct, interconnected pillars.
Grooming 2.0
Predators use online gaming lobbies, educational forums, and AI-generated avatars to build false trust over weeks or months, normalizing inappropriate conversations before making requests.
Sextortion
A rapidly rising crime where perpetrators trick minors into sharing intimate images, then use those images to financially or socially blackmail the child, causing severe psychological trauma.
Non-Consensual CSAM & Deepfakes
The creation and distribution of Child Sexual Abuse Material (CSAM), worsened by AI tools that can morph innocent social media photos into explicit deepfakes.
It is crucial to understand that under Section 11 of the POCSO Act, sexual harassment is not limited to physical touch. Showing a child explicit content online, or demanding a child transmit explicit images of themselves, constitutes a severe, non-bailable offense under Indian Law. The digital medium does not dilute the severity of the crime.
Part II: The Legal Mirror — Knowing Your Defenses
When a crisis occurs, panic is the enemy of justice. India has robust legal frameworks designed to tackle these specific digital threats, provided victims and guardians know how to invoke them quickly and correctly.
| The Digital Threat | The Indian Legal Shield | Your Immediate Action |
|---|---|---|
| Online Grooming & Harassment | POCSO Act, Sec 11 & 12 Covers non-physical sexual harassment and intent. | Do not delete chats. Take screenshots, record screen activity, and report to the National Cyber Crime Portal. ✓ Preserve Evidence |
| Morphing / Deepfakes | IT Act, Sec 66E & 67B Strict penalties for violating privacy and publishing explicit material of minors. | Use Section 67B to force platforms to immediately take down the content. ✗ Act Within 24 Hrs |
| Sextortion & Blackmail | IPC / BNS & IT Act Sec 66 Covers extortion, criminal intimidation, and computer-related offenses. | Cease communication immediately. Do NOT pay the ransom. File a zero FIR at the nearest police station. ✓ Block & Report |
Part III: Bridging the Gap — 7 Actionable Steps for 2026
Awareness without action is merely anxiety. To protect our children, we must move from a posture of fear to a strategy of resilience. Here are seven concrete, actionable ways parents, guardians, and educators can build a robust digital firewall around the youth to prevent Digital Child Sexual Exploitation.
-
01
The "Digital Consent" Dialogue
We teach children about "good touch and bad touch" in the physical world. The same must apply digitally. Teach children that their data, their photos, and their online presence belong entirely to them. If anyone online asks them to keep a "special secret" from their parents, that is an immediate red flag.
-
02
Privacy Hardening
Relying on "Incognito Mode" is a myth. Implement network-level DNS filtering on your home Wi-Fi to block explicit domains automatically. Turn off location sharing on all social media apps, and set gaming consoles to only allow voice chat with approved, known contacts.
-
03
The 24-Hour Rule
In the event of an online incident, the first 24 hours are critical. Predators rely on the child's shame to buy time. Foster an environment where a child knows they can report a mistake (like sending an inappropriate photo) without facing immediate wrath or losing their device permanently.
-
04
Technological Audits
Regularly check for "Vault Apps" (apps disguised as calculators or utilities that hide photos and chats). Review the permissions granted to installed apps. Does a simple puzzle game really need access to the device's camera and microphone?
-
05
Reporting Without Shame
Familiarize yourself with the tools of justice. If an incident occurs, call the National Cybercrime Helpline at 1930 or register a complaint at cybercrime.gov.in. The system allows for anonymous reporting to protect the identity of the minor.
-
06
School-Home Alliances
Individual parenting is not enough; we need community firewalls. Schools must integrate cyber-law literacy into the curriculum. Parents should lobby school boards to host workshops led by legal experts and cybersecurity professionals to keep the community updated on the latest app trends.
-
07
Seek Specialized Legal Recourse
If the worst happens, do not navigate it alone. Engage with the Child Welfare Committee (CWC) in your district and consult lawyers who specialize in POCSO and cyber laws. The legal system is designed to prioritize the rehabilitation and privacy of the child over all else.
The greatest weapon a predator possesses is the social stigma associated with sexual exploitation. In India, the fear of "Log kya kahenge?" (What will people say?) often stops families from filing an FIR. By staying silent, we embolden the criminal. Reporting a crime is the highest form of child protection.
"You cannot outsource the digital safety of your child to an algorithm. Vigilance is a daily practice."— Cyber Safety Mandate
The Digital Firewall Starts at Home
The threat of Digital Child Sexual Exploitation is real, adapting, and sophisticated. But it is not invincible. The laws of the land—from POCSO to the IT Act—are evolving to give victims a voice and to strike down those who prey on innocence.
Protecting our youth in 2026 requires more than just restricting screen time; it demands digital literacy, open communication devoid of shame, and an unwavering commitment to holding perpetrators accountable under the law.
Let us transform our fear into education, and our anxiety into action. Equip your children with the knowledge to identify danger, and equip yourself with the legal literacy to fight back.
Report Cybercrime Now